Reach for the Skai.
Grow your career.
Ready for your next challenge? At Skai, you’ll have the freedom to develop your skills and the support to take your career wherever you want it to go.



Our Latest Roles
Explore open roles across teams and continents


Our core values build our culture
Humility
We listen, learn and have empathy for others. Always.
Innovation
We don’t follow the pack, we lead.
Passion
We love what we do, knowing it helps our clients.
Integrity
We’re independent, unbiased and guided by the truth.
Be part of our global team
Benefits that go beyond the basics
At Skai, we offer the essentials—comprehensive medical coverage, retirement savings with company matching, and generous PTO—but it’s the opportunities for personal and professional growth that truly set us apart. From working with top tech leaders to a culture that encourages development, we’re invested in your success.
Partnering with the biggest tech leaders
Health and wellness initiatives
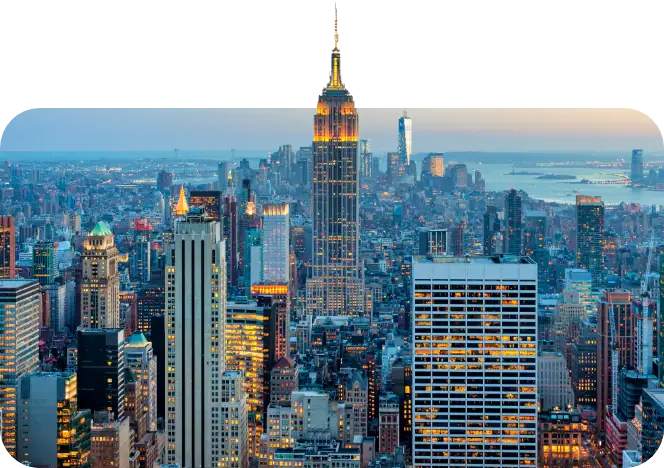
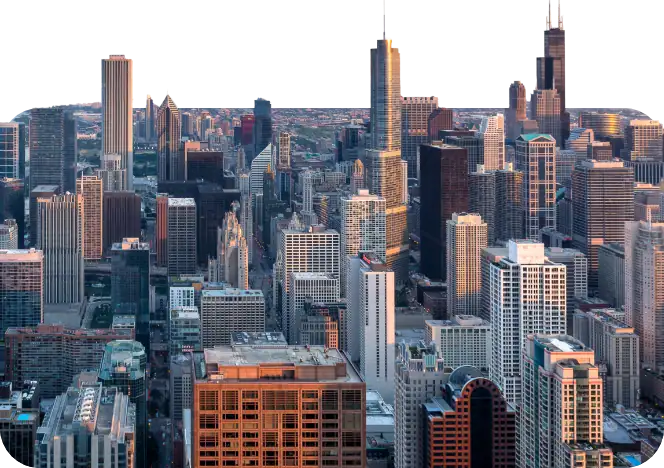
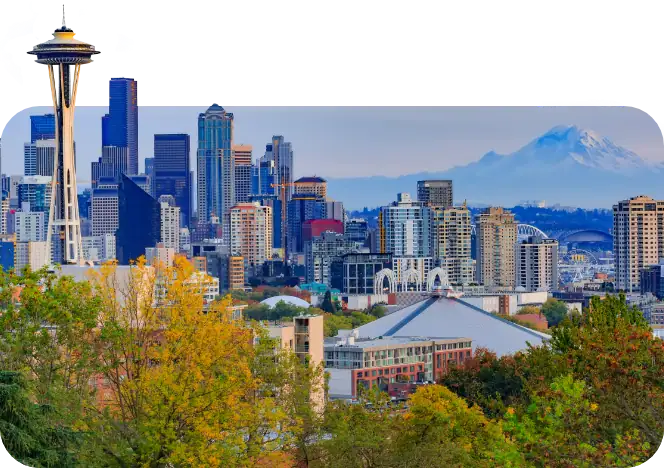
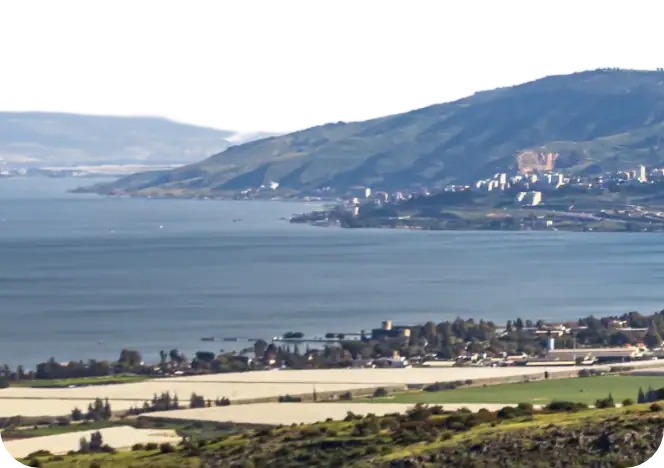
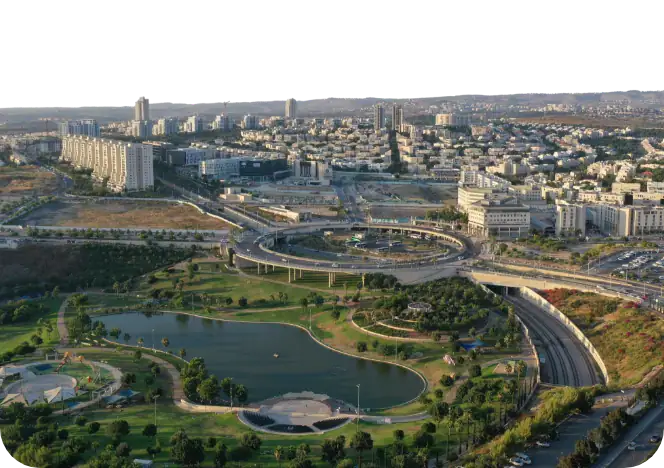
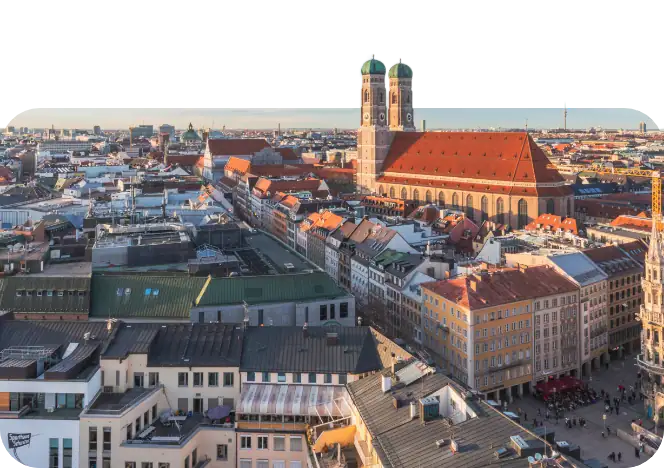
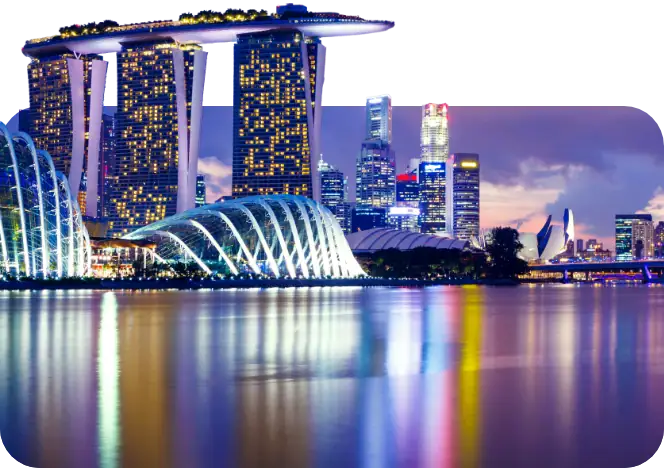
Offices in cities across the world
Employee match retirement savings
Professional growth stipend
Stock option plan
Diversity and inclusion programs
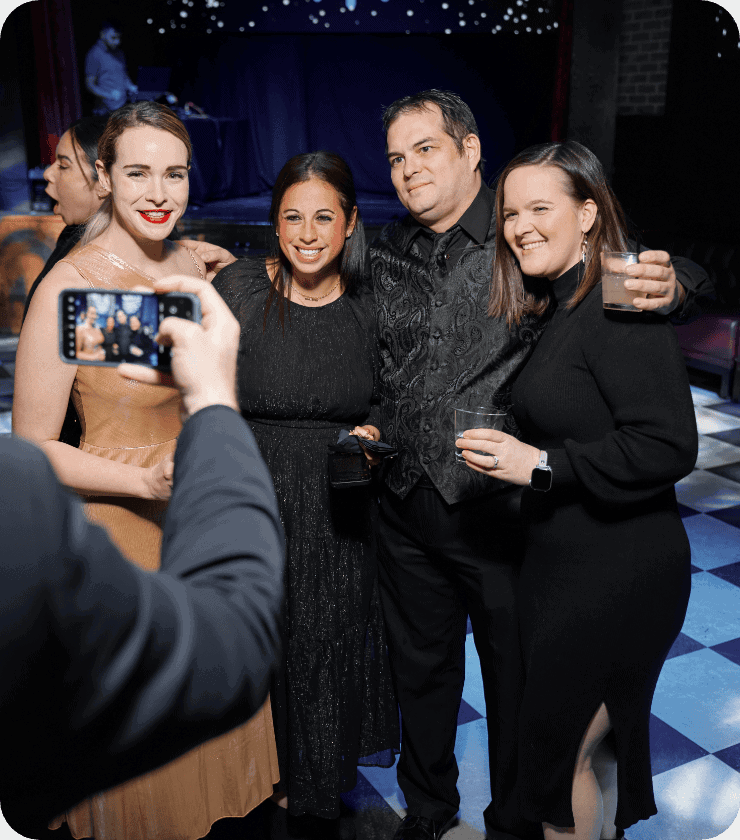
Stocked kitchens and happy hours
Company outings and volunteering
Exclusive perks and discounts
Comprehensive medical coverage
Generous paid time off

A work-life balance that works for you
At Skai, we believe a balanced life leads to better work. Our flexible, hybrid model allows you to work from the office three days a week, with the freedom to choose where you work the rest of the time. We all have lives outside of work, and Skai wants to make sure you’re living your best one.